Regulatory Standards for Data Security in Stem Cell Banking
Regulatory Standards for Data Security in Stem Cell Banking
Stem cell banking involves not just preserving biological samples, but also protecting sensitive personal and genetic data. This data includes genetic fingerprints, maternal health records, and other private information that, if exposed, could have lifelong consequences for families. Two major regulatory frameworks guide how this data is secured: HIPAA and FDA regulations in the U.S., and GDPR in the EU.
-
HIPAA (U.S.):
- Focuses on electronic health information security.
- Allows flexibility in implementing security measures like like encryption.
- Requires breach reporting and detailed risk assessments.
- Offers limited patient rights like access and amendments to records.
-
GDPR (EU):
- Covers all personal data, including genetic and health data.
- Enforces strict breach reporting within 72 hours.
- Grants individuals rights like data erasure and portability.
- Applies globally to any organization handling EU residents' data.
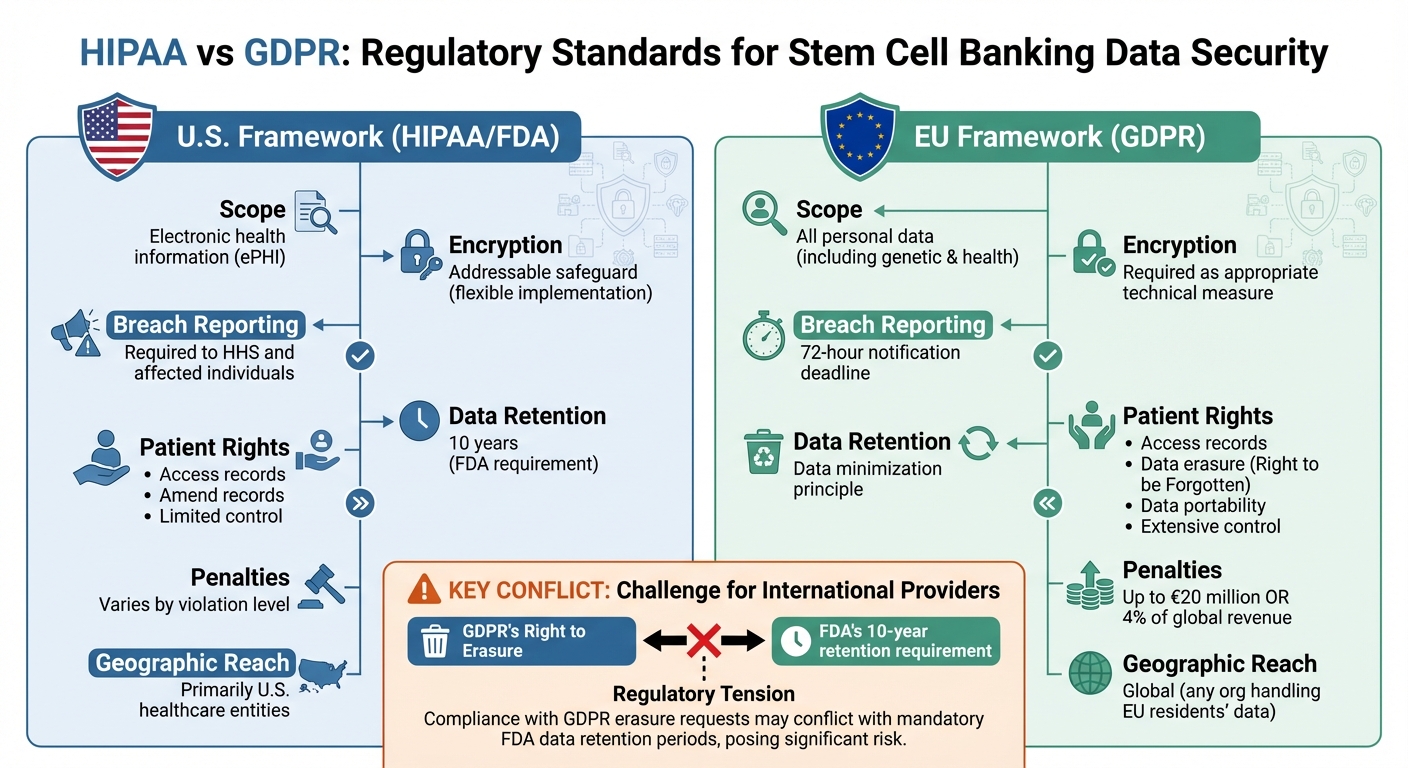
While HIPAA emphasizes healthcare-specific protections, GDPR prioritizes individual rights and privacy. For stem cell banks operating internationally, navigating these frameworks is challenging, especially where requirements like GDPR’s “Right to Erasure” conflict with FDA’s 10-year data retention rules.
Providers like Americord Registry address these challenges by combining regulatory compliance, advanced security measures, and lifetime storage guarantees. Both frameworks aim to ensure data safety, but their approaches reflect differing priorities and enforcement strategies.
HIPAA vs GDPR Data Security Standards for Stem Cell Banking
1. U.S. Regulatory Standards: HIPAA and FDA
In the U.S., stem cell banks operate under two main regulatory umbrellas: HIPAA (Health Insurance Portability and Accountability Act) and the FDA (Food and Drug Administration). HIPAA governs how facilities handle electronic protected health information (ePHI), while the FDA oversees the biological products themselves. Any stem cell bank that electronically transmits health information tied to standard transactions is considered a "covered entity" and must follow HIPAA's Security, Privacy, and Breach Notification Rules.
Flexibility in Security Measures
HIPAA's Security Rule is built to adapt to different organizations. According to the Department of Health and Human Services (HHS):
The Security Rule is designed to be flexible, scalable, and technology neutral, enabling a regulated entity to implement policies, procedures, and technologies that are appropriate for the entity's particular size, organizational structure, and risks to ePHI.
In practice, this means both small local facilities and larger organizations can tailor their security measures to fit their unique needs, especially when deciding whether to bank cord blood, tissue, and placenta. These foundational guidelines shape critical security practices, including encryption and breach protocols.
Encryption Standards
HIPAA's Security Rule (45 CFR § 164.312) classifies encryption as an "addressable" safeguard - this means facilities must assess whether encryption is the most effective way to protect their ePHI. If not, they must justify their decision and implement an alternative protective measure. This applies to both data at rest (stored data) and data in transit (data being transmitted).
Encryption transforms data into unreadable formats unless decrypted with the correct key. While HIPAA doesn't specify algorithms, facilities must ensure that ePHI remains confidential, intact, and accessible when necessary.
Breach Reporting and Incident Management
Strong breach reporting practices are a critical part of safeguarding ePHI. If unsecured health information is breached, covered entities must notify both affected individuals and the HHS Secretary. HIPAA requires facilities to implement "Security Incident Procedures" to identify and address any suspected or known breaches.
Third-party vendors, known as business associates, are also legally required to report incidents to the covered entity immediately. Additionally, facilities must keep documentation of security assessments, policies, and any actions for at least six years from their creation or last effective date.
Patient Consent Models
HIPAA differentiates between Consent and Authorization when it comes to patient permission:
- Consent is optional for routine activities like treatment, payment, and healthcare operations (TPO). Facilities can decide how to handle this.
- Authorization is required for anything outside TPO, such as research or marketing, and must follow specific guidelines.
| Feature | HIPAA Consent | HIPAA Authorization |
|---|---|---|
| Mandatory | Optional for TPO | Required for non-TPO uses (e.g., research, marketing) |
| Format | Facility discretion | Must use clear, specific language |
| Revocation | Not explicitly outlined | Must allow revocation in writing |
| Content | General permission for care | Must include detailed info, expiration, and involved parties |
For stem cell research, PHI can be used without individual authorization if an Institutional Review Board (IRB) or Privacy Board grants a waiver under specific conditions. PHI can also be shared with FDA-regulated entities for tasks like product recalls or adverse event reporting.
Audit and Risk Assessment Requirements
HIPAA's Security Rule requires facilities to implement Audit Controls - mechanisms like software or procedures that record and monitor activity in systems containing ePHI. Regular reviews of audit logs, access reports, and incident tracking are mandatory.
Facilities must also appoint a Security Official responsible for creating and enforcing security policies. A comprehensive Risk Analysis is essential to identify vulnerabilities and risks to ePHI. Tools like the HHS Security Risk Assessment Tool or the NIST HIPAA Security Rule Toolkit can help with these evaluations.
The 2013 Omnibus Final Rule added more accountability by holding business associates directly responsible for HIPAA violations. Now, third-party vendors working with ePHI face the same legal and financial consequences as the facilities themselves.
2. EU Regulatory Standards (GDPR)
In contrast to U.S. regulations, which center on electronic protected health information, the EU's General Data Protection Regulation (GDPR) takes a broader approach to protecting sensitive genetic and health data. For stem cell banks in the EU, this means adhering to stricter rules since genetic and health data fall under the "special categories of personal data" outlined in Article 9. These facilities must meet heightened requirements, focusing not only on security but also on safeguarding individual rights, which heavily influences how they handle sensitive information.
Encryption Standards
Article 32 of the GDPR requires data controllers and processors to implement "appropriate technical and organisational measures" to ensure data security. Encryption is a cornerstone of these measures, but the regulation takes a risk-based approach, allowing organizations to tailor their encryption methods based on factors like the latest technology, implementation costs, and the specific nature of the data processing.
"The controller and the processor shall implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk, including... the pseudonymisation and encryption of personal data." - Art. 32 GDPR
Interestingly, if a stem cell bank uses strong encryption and ensures the security of encryption keys, any data breach might not need to be reported. This is because the encrypted data would remain inaccessible to unauthorized parties, giving organizations some flexibility to adopt encryption methods that align with their unique risks and capabilities.
Breach Reporting Timelines
GDPR enforces a strict 72-hour window for breach notifications, making it one of the most demanding frameworks worldwide. Data controllers must inform the supervisory authority within this timeframe after discovering a breach. If the breach poses a "high risk" to individuals' rights and freedoms - a likely scenario in stem cell banking due to the sensitivity of genetic data - the facility must also notify affected individuals promptly.
Third-party processors, such as labs or storage vendors, are required to inform the data controller immediately upon detecting a breach. Additionally, facilities must maintain detailed records of breaches, including their impact, the steps taken to address them, and preventative measures. Falling short of these obligations can lead to severe penalties.
Patient Consent Models
Under GDPR, consent must be "informed", "specific", and "unambiguous", empowering individuals to retain control over their personal data. Beyond basic permission, the regulation includes the Right to be Forgotten, allowing individuals to request the deletion of their data. For stem cell banks, this presents a challenge: balancing long-term storage requirements with the rights of patients.
Genetic data, such as HLA and STR profiles used in stem cell banking, is considered "unique data" that could potentially re-identify donors even if anonymized. GDPR ensures that such sensitive data cannot be made publicly available unless the donor explicitly consents. Importantly, U.S.-based companies offering services to EU residents must also comply with GDPR, regardless of their physical location.
Audit Requirements
Article 32 also mandates that organizations establish a process for "regular testing and evaluation" of their security measures. This isn't a one-time obligation - facilities must perform ongoing reviews of their technical protections and document the results. Every breach must be logged in detail, allowing authorities to verify compliance with reporting and security obligations.
Non-compliance with GDPR can result in severe financial penalties. Organizations face fines of up to €20 million or 4% of their global annual revenue, whichever is higher. In the first 20 months following GDPR's implementation, regulators imposed over €114 million in fines, underscoring the seriousness with which the EU enforces these regulations.
Advantages and Disadvantages
Understanding the strengths and challenges of U.S. and EU frameworks helps stem cell banks navigate compliance while protecting patient data effectively.
In the U.S., HIPAA and FDA regulations provide a flexible, healthcare-oriented approach (45 CFR § 164.306). This allows facilities - big or small - to tailor their security measures based on their resources, ensuring they still capture the benefits of cord blood banking. However, this flexibility comes with limitations. HIPAA is primarily designed for U.S. healthcare data, offering minimal protections for international operations. While patients can access and amend their records, they lack broader controls like data deletion or portability, which are available under European standards.
On the other hand, the EU's GDPR offers sweeping protections that apply internationally. Any organization handling the data of EU residents must comply, regardless of where it's based. GDPR goes further by granting individuals rights like data erasure and portability, giving them more control over their personal information. However, these protections can create logistical hurdles. For instance, GDPR's "Right to Erasure" can clash with the FDA's 10-year data retention requirement, creating compliance headaches for organizations operating in both regions. Non-compliance can also be costly - GDPR fines can reach €20 million or 4% of global revenue, as demonstrated by recent high-profile penalties.
| Feature | U.S. Framework Advantage | EU Framework Advantage |
|---|---|---|
| Implementation | Flexible, adaptable to facility size and resources | Consistent, high standards across all organizations |
| Scope | Focused on clinical safety and traceability | Broad coverage of all personal data types |
| Patient Control | Rights to access and amend records | Rights include erasure and portability |
| International Operations | Primarily domestic compliance | Global applicability for EU residents' data |
| Record Keeping | 10-year retention ensures long-term traceability | Data minimization limits storage to essentials |
Conclusion
The regulatory environment for stem cell banking data security is shaped by two distinct models. In the U.S., the framework is grounded in HIPAA and FDA regulations (21 CFR Part 1271), which prioritize clinical safety and privacy, requiring providers to retain records for at least 10 years. Meanwhile, the EU's GDPR emphasizes data protection rights like erasure and portability, with enforcement penalties reaching up to €20 million or 4% of global revenue. For families banking their newborn's stem cells, providers operating across borders face the challenge of balancing the FDA's stringent product safety requirements with the GDPR's robust privacy protections. This becomes particularly complex when the GDPR's "Right to Erasure" clashes with the FDA's retention mandates for tissue tracking and donor eligibility.
Americord Registry addresses these challenges through a comprehensive compliance strategy. The company holds FDA registration, AABB accreditation, and state-specific licenses in jurisdictions like New York, California, and Illinois. Its laboratory operates with 24/7 monitoring and stores stem cells at –196°C in liquid nitrogen tanks, ensuring both physical and digital security meet rigorous standards.
"We have consistently defined the highest standards in the industry through scientific innovation, customer service, and total transparency." – Americord Registry
With more than 80 FDA-approved treatments utilizing cord blood stem cells and studies confirming the long-term viability of these cells, Americord Registry demonstrates a commitment to compliance on both national and international levels. Backed by a $110,000 engraftment guarantee - the highest in the industry - its approach combines robust accreditation, state-of-the-art monitoring, and financial safeguards, giving families peace of mind by balancing clinical safety with strong data privacy protections.
FAQs
What are the key differences between HIPAA and GDPR in protecting data for stem cell banking?
When it comes to safeguarding data in stem cell banking, HIPAA and GDPR serve different purposes and apply to distinct regions.
HIPAA (Health Insurance Portability and Accountability Act) is a U.S.-specific regulation designed to protect individuals' health information. It mandates strict privacy and security measures, especially for electronic health records. HIPAA applies exclusively to healthcare organizations operating within the United States.
GDPR (General Data Protection Regulation), by contrast, is a European Union law that governs the handling of any personal data, including health-related information. Its focus is on individual rights, emphasizing key principles like user consent, data minimization, and the right to access or delete personal data. GDPR applies to any entity processing data from EU residents, no matter where the organization is based.
In short, HIPAA zeroes in on healthcare data security within the U.S., while GDPR takes a broader approach, addressing all types of personal data and prioritizing user control and consent.
What are the main challenges stem cell banks face in meeting both HIPAA and GDPR requirements?
Stem cell banks encounter tough hurdles when trying to meet the requirements of both HIPAA (Health Insurance Portability and Accountability Act) and GDPR (General Data Protection Regulation). These two frameworks, while aimed at protecting sensitive information, have distinct focuses. HIPAA, relevant in the United States, prioritizes safeguarding health data through measures like encryption, strict access controls, and mandatory breach notifications. On the other hand, GDPR, which applies to the personal data of EU citizens, takes a broader approach. It stresses the importance of explicit consent, limiting data collection to what's necessary, and allowing individuals the right to request their data be erased.
Handling cross-border data transfers is another layer of complexity. Stem cell banks must ensure that sensitive donor and patient data remains secure while adhering to both sets of regulations. This often means implementing cutting-edge encryption methods and developing comprehensive privacy policies. Successfully navigating these regulatory demands requires systems designed to handle diverse rules and a serious focus on maintaining data security and compliance.
Why is encryption essential for securing data in stem cell banking?
Encryption plays a key role in stem cell banking by securing sensitive personal and medical information. By converting this data into an unreadable format, encryption ensures that unauthorized users cannot access or misuse it, keeping donor information safe and private.
Additionally, encryption helps stem cell banks meet strict regulatory standards for data security and privacy. This not only protects individuals but also reinforces trust in the reliability and safety of stem cell banking services.
The views, statements, and pricing expressed are deemed reliable as of the published date. Articles may not reflect current pricing, offerings, or recent innovations.